Security Considerations For Cloud Architectures
April 15, 2024
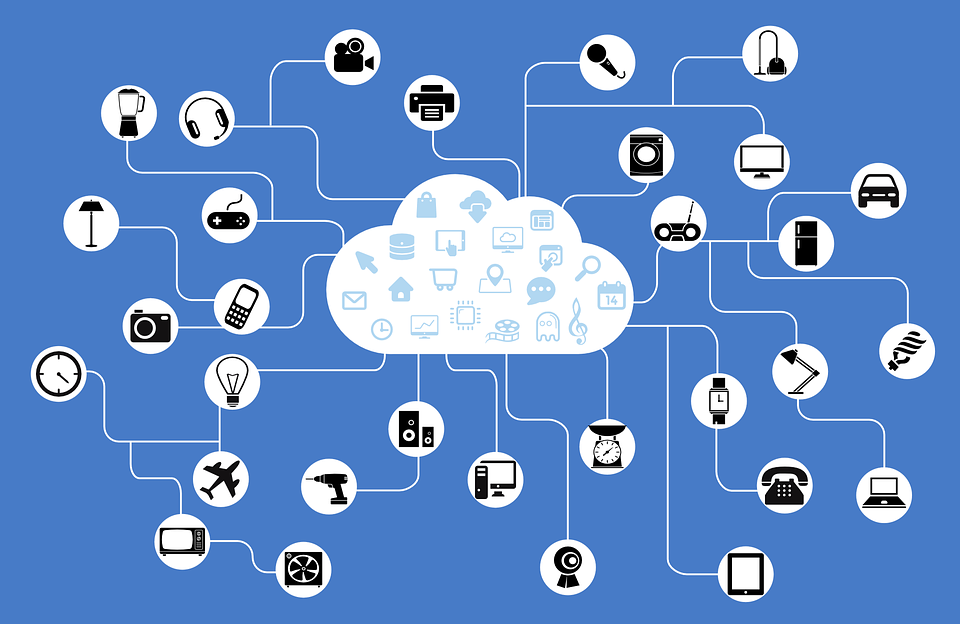
The shift from server to cloud computing is bringing new levels of efficiency to businesses and organizations. However, there is a simultaneous increase in security threats as well. Large amounts of data stored on the cloud makes it a lucrative target for hackers and people with malicious intents. Before we shift to cloud computing and reap its efficiency benefits, it is necessary to consider the security challenges and take proper measures to safeguard our organizations’ and clients’ data. In the following paragraphs, we will discuss the three most important security issues in the context of cloud computing.

Data Breach
A data breach occurs when an unauthorized person views, steals and releases confidential information. A data breach may occur due to an intentional effort of persons, or it may be a result of human error, inadequate security, or vulnerable applications. Common examples of a data breach include financial information, personal health information, personal files, and business secrets.
Data stored on cloud solutions may have value to different people due to different reasons. Financial gain is one of the biggest motives for hackers to break into cloud systems. In addition to financial frauds, rival companies sometimes try to break into competitor’s corporate or cloud systems to gain access to trade secrets and intellectual property. Activists aim to gain access to data to expose information.
Security considerations for cloud architectures apply to traditional corporate networks as well. However, shared resources and large amounts of data make cloud computing a prime target of data breaches. The impact of data breaches is very significant but difficult to measure. A data breach causes loss of repute, loss of business, and legal complications for affected organizations.
Insufficient Management: Identity, Credentials, and Access
Insufficient identity, credential, and access management is a major security concern and a cause of data breaches. Best security practices must be employed to minimize such security threats. These practices include strong passwords, multifactor authentication, and regular automated rotation of cryptographic keys and certificates.

Key management activities should be ensured by secured public key infrastructure (PKI). Sensitive information and cryptographic keys should not be embedded in source code due to the risk of misuse. Identity management system of organizations should support timely de-provisioning of access to the system in case of personnel changes like job a change.
Federating identity with cloud provider is rising. It is necessary for the organizations to understand the security of cloud provider’s solutions. These solutions include infrastructure, processes, and segmentation implementation for shared cloud solutions.
Multifactor authentication can mitigate the risk of damage due to password theft. In cases where multifactor authentication is not always possible, strong password and password rotation policies should be enforced. Furthermore, cryptographic keys used to protect data access should be rotated periodically. Passwords stored in a central location are a high-value target for hackers and must be protected like any high-value asset.
System Vulnerabilities
Computer software has always been subject to bugs and vulnerabilities. Any software is secure as far as the vulnerabilities remain undiscovered. Once discovered, system vulnerabilities can be used to infiltrate systems to take control of the system or steal private data. In cloud computing, systems are placed in close proximity and many organizations share the resources of the same system creating new avenues of attack.
IT best practices can go a long way to mitigate such attacks. Keeping an eye on discovered system vulnerabilities and applying patches and updates in a timely manner should be a fundamental security practice. Security considerations include a well-though for cloud architecture and design with security as a primary concern. A well-thought and well-implemented design can even shield the systems from new and emerging threats.
This is certainly not an exhaustive list of security considerations. Insecure APIs, malicious insiders, data loss, abuse and nefarious use of cloud services, account hijacking, and denial of service are some other important issues to consider.

Peter is a friendly, knowledgeable writer and blogger who loves to share their knowledge of technology. He enjoys writing about the latest gadgets and gizmos as well as other information on how to use them. He has been blogging for years now, but he still loves it just as much as he did when he started!